This website stores cookies on your computer.
These cookies are used to collect information about how you interact with our website and allow us to remember you. We use this information in order to improve and customize your browsing experience and for analytics and metrics about our visitors both on this website and other media. To find out more about the cookies we use, see our Privacy Policy.

Connection and HP Celebrate 30 Years of Innovation. Learn More
Servers
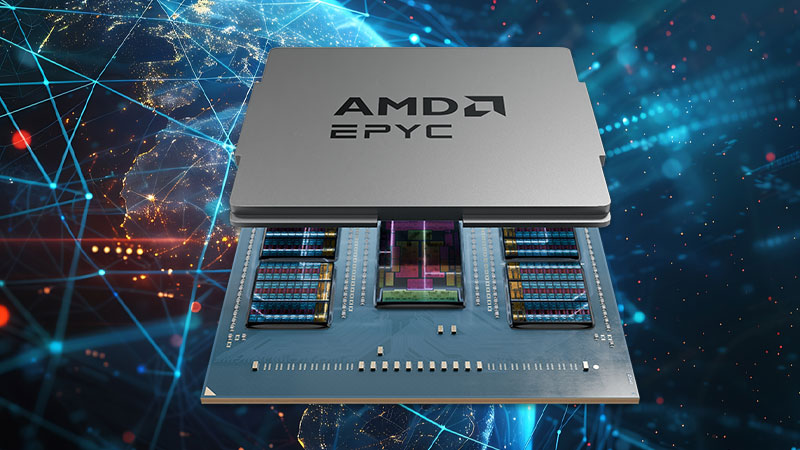
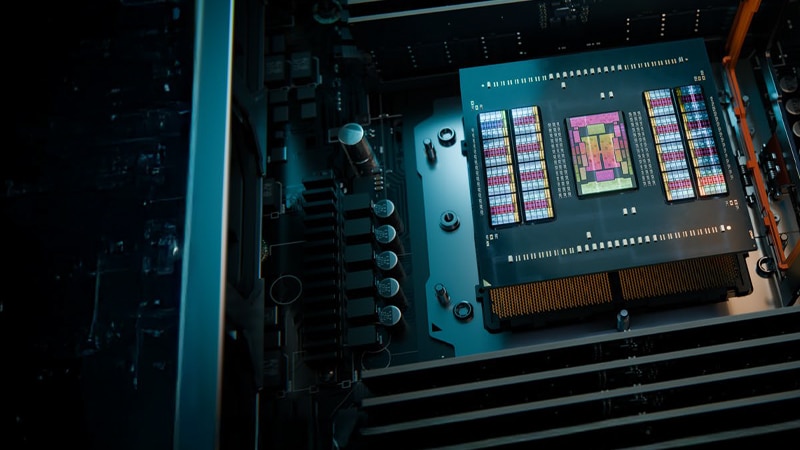
Introducing the 5th Generation AMD EPYC™ 9005 Series Processors
Peak Performance for Cloud, Enterprise, and AI
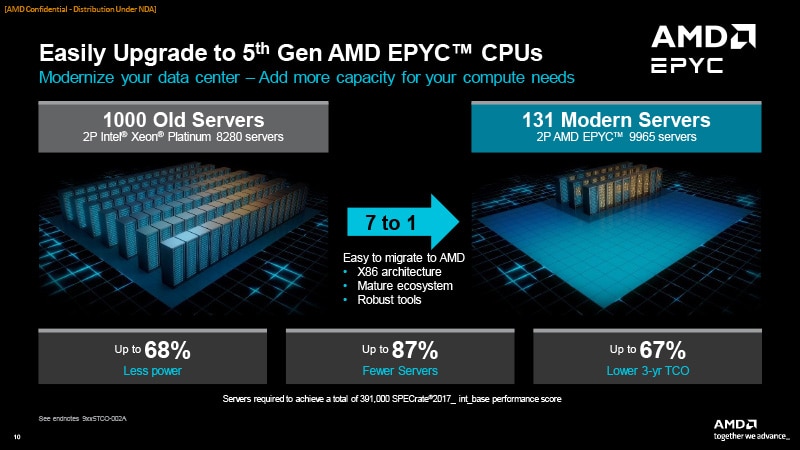
The AMD EPYC™ 9005 Series Processors are designed to deliver exceptional performance, density, and efficiency to support the most demanding data center initiatives. With up to 192 cores, these processors are built on the innovative Zen 5 and Zen 5c architectures, providing industry-leading performance and energy efficiency.- Up to 17% IPC for enterprise and cloud applications
- Up to 37% IPC for HPC and AI
- Up to 86% fewer servers required, with 7:1 consolidation capacity
- Up to 69% less power use
- Up to 64% lower 3-year TCO

The Future of AI in Data Centers Introducing 5th Generation AMD EPYC™ Processors
AMD EPYC™ Processors already offer uncompromising performance and efficiency. So, what happens when AMD improves upon an already powerful product? Let AMD expert Jim Greene, Director of Server Product Marketing at AMD, walk you through what 5th Generation AMD EPYC™ Processors can do for your business.6 Compelling Reasons IT Managers Should Consider Modernizing to AMD EPYC™ Processors
Today’s IT managers face immense pressure for a variety of reasons: they need to activate new revenue streams, develop strategies to support changing workforce requirements, and integrate new capabilities to improve efficiency within the business. While upgrading to new servers can alleviate these issues, cost is often perceived by many as a barrier.AMD EPYC™ 5th generation processors boost performance, consolidate servers, and optimize software licensing costs. Read this blog to learn how you could recoup your investment in as little as two months.
Power Your AI Revolution
53% of businesses already apply AI to improve production processes, and 51% are adopting AI for process automation.* With their leadership performance, exceptional energy efficiency, and built-in security capabilities, AMD EPYC™ Processors can be critical to enabling artificial intelligence solutions, extending and enriching workloads and activities across industries and organizations of all sizes.Discover how AMD EPYC™ 9005 Series processors can transform your data center and drive business forward. Check out the detailed infographic for an in-depth look at the features and benefits of these powerful processors.
Choose to Advance with AMD EPYC™ Processors
AMD EPYC™ Processors are the ideal choice for modernizing IT infrastructure, driving business-critical initiatives, and navigating the constantly evolving technological landscape while maintaining a competitive edge. And given AI’s transformative role, it is now essential to equip your data center to efficiently handle AI workloads. Learn how AMD EPYC™ Processors support demanding AI workloads, enhance enterprise applications, and provide robust security features with AMD Infinity Guard.Download the white paper now to gain in-depth insights and stay ahead in the rapidly evolving tech landscape.

A Trusted Choice for Small Business and Hosted Services Embracing the AI Era
AMD EPYC™ 4005 processors extend the broad AMD EPYC processor family, powering a new line of entry level systems designed for small business customers and hosted IT services providers that demand performance, advanced technologies, energy efficiency, and affordability.Announcing AMD EPYC™ 4005 Processors
If you’re part of a small or medium-sized business, you know the pressure to do more with less—especially when it comes to IT. That’s why AMD is excited to share the launch of the AMD EPYC™ 4005 Series processors—designed specifically for SMBs that need enterprise-grade performance without the enterprise-sized price tag.Interested in seeing how AMD and Connection can help your business? Contact us today!

AMD EPYC™ 4005 Series Processors
Affordable Server Solutions for Growing Businesses
AMD EPYC™ 4005 Series processors empower small businesses and hosting providers with advanced technology in energy-efficient and affordable systems. Delivering high performance at an attractive price, these processors offer scalability and efficiency for building fast, practical solutions. Whether you’re a small business, dedicated hosting provider, or technology provider, AMD EPYC 4005 processors power turnkey, easy-to-use, and manageable server solutions, propelling business growth and success in the AI era.
AMD EPYC 4005 for Hosting
AMD EPYC 4005 for Edge Computing
AMD EPYC 4005 for SMB
AMD EPYC™ Processors in Action
Case Studies
AMD Enhances Nissan’s Crash Test Simulation Performance
Nissan experienced 30 percent better performance by switching vehicle crash testing workloads to Microsoft Azure VMs powered by AMD EPYC™ CPUs.
Unlocking AI for R&D
To supercharge its research and development development efforts with Al, Sunplus Innovation Technology deployed Lenovo ThinkSystem servers, powered by AMD EPYC™ 7003 Series processors, and ThinkSystem storage—giving the company the capacity and performance to harness new AI applications.
Atman Offers Flexible, Market-leading Data Center Services with Lenovo
Using Lenovo ThinkSystem servers, powered b y AMD EPYC™ processors, Atman enhances its client offerings and improves its agility and environmental performance, and becomes the first company in Poland to achieve Lenovo Cloud Service Provider status.
Experience the Difference AMD EPYC™ Processors Make
See the performance and efficiency of AMD EPYC™ Processors in action. Fill out the form below to request an assessment, and we will be in touch to help you find the right EPYC Processor to meet your business needs.Thank You for submitting your request!
We’ll review your information and have someone contact you shortly.
*Forbes Advisor, “How Businesses Are Using Artificial Intelligence In 2023,” April 24, 2023
AMD, the AMD Arrow logo, [add used AMD trademarks in alphabetical order as necessary] and combinations thereof are trademarks of Advanced Micro Devices, Inc.
AMD, the AMD Arrow logo, [add used AMD trademarks in alphabetical order as necessary] and combinations thereof are trademarks of Advanced Micro Devices, Inc.